Speech emotion recognition (SER) is rapidly emerging as a pivotal technology across a variety of sectors, including healthcare, security, and human-computer interaction. This cutting-edge application leverages deep learning models, such as convolutional neural networks (CNN) combined with long short-term memory networks (LSTM), to identify emotional cues from voice intonations. However, as with most innovations rooted in deep learning, SER systems face significant challenges, particularly from adversarial attacks—deliberate perturbations in input data aimed to mislead these models. The study conducted by researchers at the University of Milan sheds light on this issue, unveiling the vulnerabilities of SER systems to various attack methodologies.
Adversarial attacks can be categorized primarily into white-box and black-box attacks, each distinguished by the level of access the attacker has to the model’s parameters. White-box attacks occur when the attacker has knowledge of the model architecture and its parameters, allowing them to craft highly disruptive inputs. Black-box attacks, in contrast, involve minimal information about the model and rely solely on its output to generate adversarial examples. The recent findings in the Milan study indicate that both types of attacks significantly undermine SER systems. However, what is particularly startling is the effectiveness of black-box attacks, which, even without understanding the model’s internal mechanics, managed to achieve commendable success rates.
The Research Study: Methodology and Findings
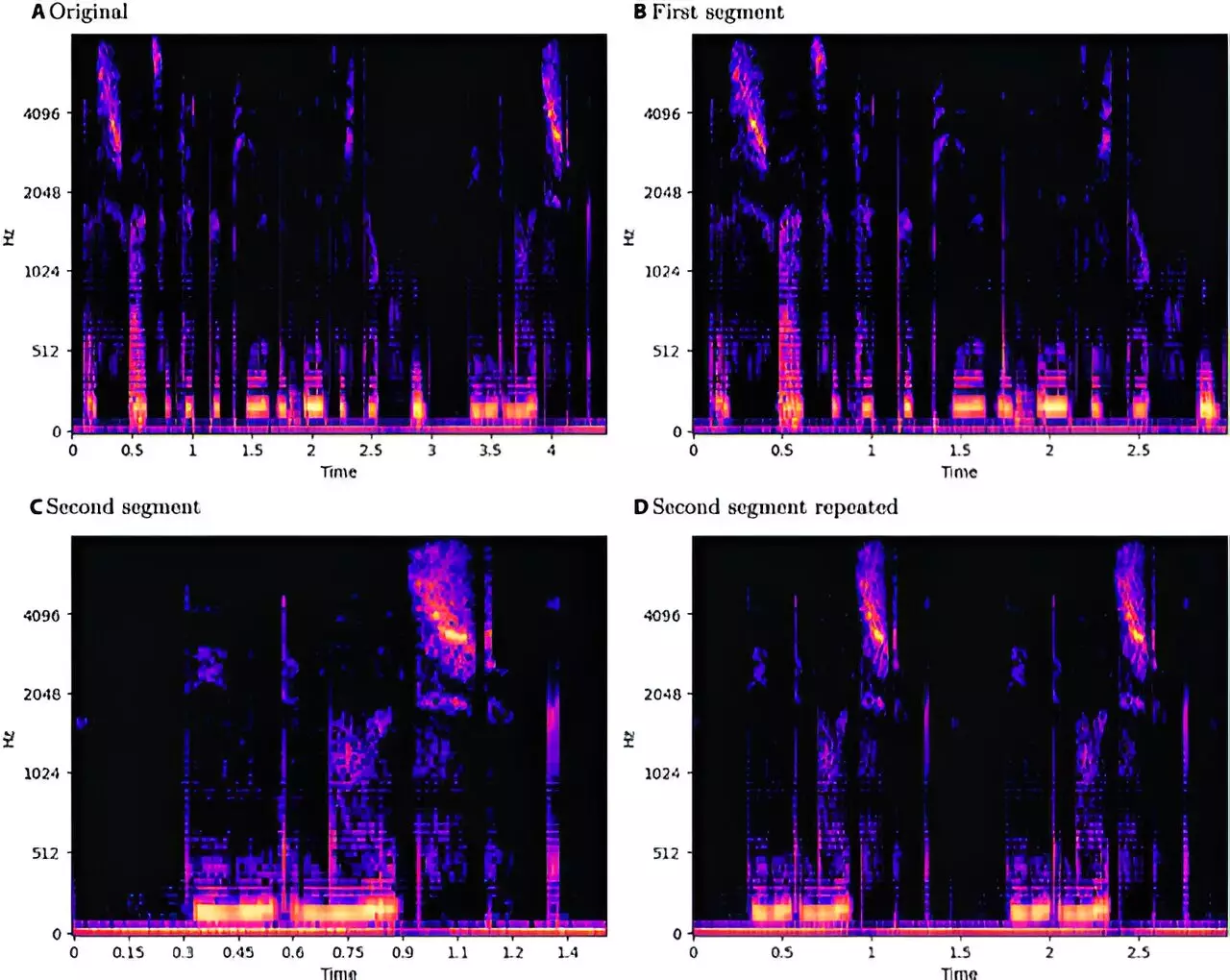
Conducted under a rigorous experimental framework, the study examined three primary datasets representing different linguistic backgrounds: EmoDB (German), EMOVO (Italian), and RAVDESS (English). The researchers implemented several known adversarial attack strategies, such as the Fast Gradient Sign Method and DeepFool for white-box scenarios, alongside black-box techniques like the Boundary Attack. Among the critical observations was that while white-box attacks exhibited considerable performance drops in SER accuracy, the black-box attacks often emerged with fewer disruptions to the system’s functioning. This revelation poses a serious threat, suggesting that an attacker could successfully exploit systems in practical settings with minimal knowledge.
Gender and Language Influence
In addition to examining the technical vulnerabilities of SER systems, the research also focused on gender differences in emotional speech processing. Interestingly, while the differences were subtle, the analysis indicated male speech samples tended to showcase slightly less accuracy when subjected to white-box attacks. This facet of the study highlights another layer of complexity within SER technology; not only do the adversarial attacks pose threats, but they also interact with inherent biases that may exist based on gender and language. The Italian dataset reflected the least susceptibility to attacks, suggesting that certain linguistic contexts might offer better resilience against adversarial perturbations.
The revelations from the University of Milan’s work underline an essential paradox in the field of machine learning research: the necessity for transparency. While it may be tempting to keep vulnerabilities under wraps for security reasons, exposing weaknesses can foster a beneficial cycle of improvement. By making these vulnerabilities public, researchers can work collaboratively to bolster SER systems’ defenses against potential threats. It is through the open dialogue between researchers and practitioners that the technological landscape can evolve towards enhanced security measures.
The vulnerabilities highlighted by the Milan study expose critical flaws in the current implementation of speech emotion recognition technologies. As SER systems become more widespread across various applications, the implications of their susceptibility to adversarial attacks cannot be understated. The continuous evolution of attack methodologies demands an equally adaptive response in defense mechanisms. A culture of transparency and collaboration within the research community is essential for developing robust systems that can withstand the challenges posed by maleficent parties. Understanding these vulnerabilities is the first step toward creating resilient SER technologies capable of serving society’s needs without compromising security. In a world where communication is increasingly mediated by machines, safeguarding the integrity of these systems is not just wise but imperative.
Leave a Reply